Generate 1024 Bit Key Cisco Command
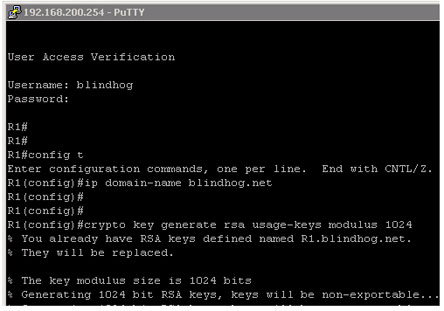
Jun 11, 2019 SW1 ( config)# crypto key generate rsa. How many bits in the modulus 512: 1024% Generating 1024 bit RSA keys, keys will be non-exportableOK Set the size of key to 1024 bits. If your Cisco Switch is running an older version of Cisco IOS image, then it is extremely recommended that you upgrade to latest Cisco IOS. Mar 30, 2020 I have set DNS domain name with “IP domain-name” command. Then configure the router to use RSA key pair with modulus size of 1024 bites for remote service authentication with “crypto key generate rsa ” command. Add username “Admin” with Password of “Technig” for ssh authentication. Enabled ssh with “line vty 0 4” command. Crypto key generate rsa exportable modulus 1024% The key modulus size is 1024 bits% Generating 1024 bit RSA keys, keys will be exportable.OK despues quiero enrolar. Crypto ca enroll CERTIFICADO. Pero al enrollar mi terminal genera una llave de 512 bits. Porque puede ser eso? Mi equipo es un cisco 1811 flash:c181x-advipservicesk9-mz. How I create RSA key and enable SSH access in Cisco VG202, in a Cisco router I use the next commands(but in a VG not exists): conf t crypto key generate rsa modulus 1024 ip domain-name domain-name ip ssh version 2 ip ssh time-out 120 ip ssh authentication-retries 3 line vty 0 4 transport input telne.
What is the OID needed to generate a ssh crypto key on a Cisco switch or router running IOS using snmpset? Oid to generate crypto key. Command line, with the. R1(config)# crypto key generate rsa modulus 1024 The name for the keys will be: R1.CCNA-lab.com% The key modulus size is 1024 bits% Generating 1024 bit RSA keys, keys will be non-exportable. OK (elapsed time was 2 seconds) R1(config)#.Jan 31 17:54:16.127:%SSH-5-ENABLED: SSH 1.99 has been enabled Step 7: Secure the console and VTY lines. You can set the router to log out of a.
Privacy Overview
Necessary cookies are absolutely essential for the website to function properly. This category only includes cookies that ensures basic functionalities and security features of the website. These cookies do not store any personal information.
Generate 1024 Bit Key Cisco Command Download
Any cookies that may not be particularly necessary for the website to function and is used specifically to collect user personal data via analytics, ads, other embedded contents are termed as non-necessary cookies. It is mandatory to procure user consent prior to running these cookies on your website.
Introduction
This document describes how to generate 2048 bit key support for Certificate Signing Request (CSR) on the Cisco IronPort Encryption Appliance (IEA).
Configure
Most of the Certificate Authorities (CAs) have stated an explicit request to have all CSRs generated with a key pair of length 2048 bit. By default, IEA Version 6.5 uses 1024 bit key length for key pair generation. In order to force the IEA to generate a key pair of length 2048, use the keytool command as described here.
Generate a Certificate
- Log in to the IEA CLI
- At the main menu, type x in order to drop into the shell.
- Change to the root user:
- Execute the keytool in order to create a new keystore:
- Execute the keytool in order to create a CSR File:
- Provide the CSR file to the Certificate Authority in order to generate a certificate. Ensure you submit it as an Apache Web Server Certficate Signing Request.
- After you receive the .cer file from the CA, proceed to the next steps.
Import a Certificate
Note: The password used when you generate the CSR must match the keystore password in order for these procedures to work. If the CSR was created off-box, the password inputted must match the keystore password in order for these procedures to work.
You must chain the Certificate correctly
- Each CA Certificate must be extracted from the CER file received from the CA and then merged together in a text editor.
Note: This is easiest done from a Microsoft Windows machine. Other operating systems work but are more difficult to extract.
Certificates must be chained in this order: 1.Domain 2. Intermediate 3.Root- Double-click in order to open the Certificate file (.CER file), and then click the Certification Path tab:
- Start with the mid-level of the Certification Path, click the Details tab, click Copy to File, and then name it 1.CER.
- Select Base-64 encoded X.509(.CER).
- Repeat for the Top Level CA, and name it 2.CER.
- Repeat for the server certificate, and name it 3.CER.
- Use a text editor (not notepad, but notepad++ works well) in order to open all three X.CER files and combine them in order (1 at the top, and 3 at the bottom):
Note: There should be no empty lines between certificates and no empty line at the bottom.
- Save as <servername>.CER.
- Upload the <servername>.CER file to the IEA at /home/admin/<servername.cer> with FTP or SCP.
- Copy /home/admin/<servername.cer> to /usr/local/postx/server/conf:
- Double-click in order to open the Certificate file (.CER file), and then click the Certification Path tab:
- Use the IEA GUI in order to import the certificate [Keys and Certificates SSL Setup].
Note: Keystore = [Install Directory]/conf/enterprisenamestore.keystore or the current name of your keystore file.
Certificate = /usr/local/postx/server/conf/NEWCERT.CER.- Check Trust CA Certs.
- Click Import Certificate
- Check Trust CA Certs.
- (Optional -- If a new keystore must be created). From the IEA GUI, tell the IEA to use the new keystore:
- Choose Configuration Web Server and Proxies Web Server Connection Listeners HTTPS
- Type in the path to the new keystore file:
Example: ${postx.home}/conf/2013_5_13.keystore
- Choose Configuration Web Server and Proxies Web Server Connection Listeners HTTPS
- Deploy Changes and restart the SMTP Adapter.
Verify
There is currently no verification procedure available for this configuration.
Troubleshoot
Generate 1024 Bit Rsa Key
There is currently no specific troubleshooting information available for this configuration.