Linux Generate Pre Shared Key
There are so many benefits of using a VPN (Virtual Private Network), some of which include keeping you safe on the internet by encrypting your traffic and helping you to access blocked content/sites/web applications from anywhere. Not to mention, VPN also helps you to browse the internet anonymously.
In this article, you will learn how to quickly and automatically set up your own IPsec/L2TP VPN server in CentOS/RHEL, Ubuntu, and Debian Linux distributions.
Prerequisites:

The Wireshark WPA Pre-shared Key Generator provides an easy way to convert a WPA passphrase and SSID to the 256-bit pre-shared ('raw') key used for key derivation. Type or paste in your WPA passphrase and SSID below. Wait a while. The PSK will be calculated by your browser. Javascript isn't known. Jun 22, 2016 Under GroupVPN Client tab, if “Use Default Key for Simple Client Provisioning” option is enabled the Global VPN client will automatically fetch the Pre-shared Key when connecting to a SonicWALL Security Appliance, and hence will not prompt for it. Apr 03, 2020 Generating a strong pre-shared key A pre-shared key (also called a shared secret or PSK) is used to authenticate the Cloud VPN tunnel to your peer VPN gateway. As a security best practice, it's.
Linux A Pre-Shared Key (PSK) or also known as a shared secret is a string of characters that is used as an authentication key in cryptographic processes. A PSK is shared before being used. You can generate an SSH key pair directly in cPanel, or you can generate the keys yourself and just upload the public one in cPanel to use with your hosting account. When generating SSH keys yourself under Linux, you can use the ssh-keygen command.
A Pre-Shared Key (PSK) or also known as a shared secret is a string of characters that is used as an authentication key in cryptographic processes. A PSK is shared before being used and is held by both parties to the communication to authenticate each other, usually before other authentication methods such as usernames and passwords are applied. You can generate an SSH key pair directly in cPanel, or you can generate the keys yourself and just upload the public one in cPanel to use with your hosting account. When generating SSH keys yourself under Linux, you can use the ssh-keygen command. To do so follow these steps: Open up the Terminal; Type in the following command.
- A fresh CentOS/RHEL or Ubuntu/DebianVPS (Virtual Private Server) from any provider such as Linode.
Setting Up IPsec/L2TP VPN Server in Linux
Pre Shared Key Generator
To set up the VPN server, we will use a wonderful collection of shell scripts created by Lin Song, that installs Libreswan as the IPsec server, and xl2tpd as the L2TP provider. The offering also includes scripts to add or delete VPN users, upgrade the VPN installation and much more.
First, log into your VPS via SSH, then run the appropriate commands for your distribution to set up the VPN server. By default, the script will generate random VPN credentials (pre-shared key, VPN username, and password) for you and display them at the end of the installation.
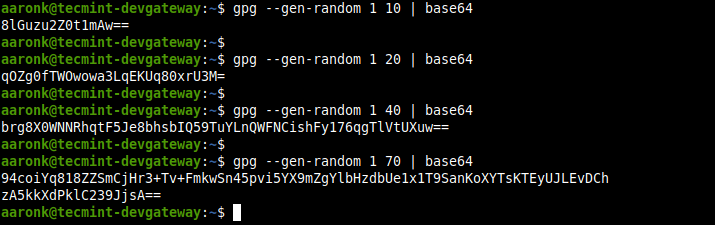
However, if you want to use your own credentials, first you need to generate a strong password and PSK as shown.
Next, set these generated values as described in the following command all values MUST be placed inside ‘single quotes‘ as shown.
- VPN_IPSEC_PSK – Your IPsec pre-shared key.
- VPN_USER – Your VPN username.
- VPN_PASSWORD – Your VPN password.
The main packages that will be installed are bind-utils, net-tools, bison, flex, gcc, libcap-ng-devel, libcurl-devel, libselinux-devel, nspr-devel, nss-devel, pam-devel, xl2tpd, iptables-services, systemd-devel, fipscheck-devel, libevent-devel, and fail2ban(to protect SSH), and their respective dependencies. Then it downloads, compiles and installs Libreswan from source, enables and starts the necessary services.
Once the installation is complete, the VPN details will be displayed as shown in the following screenshot.
Setup Your Own IPsec VPN Linux Server
Next, you need to set up a VPN client, for desktops or laptops with a graphical user interface, refer to this guide: How To Setup an L2TP/Ipsec VPN Client on Linux.
To add the VPN connection in a mobile device such as an Android phone, go to Settings–>Network & Internet (or Wireless & Networks–>More) –>Advanced–>VPN. Select the option to add a new VPN. The VPN type should be set to IPSec Xauth PSK, then use the VPN gateway and credentials above.
How to Add or Remove a VPN User in Linux
To create a new VPN user or update an existing VPN user with a new password, download and use the add_vpn_user.sh script using the following wget command.
To delete a VPN user, download and use the del_vpn_user.sh script.
How to Upgrade Libreswan Installation in Linux
You can upgrade the Libreswan installation using the vpnupgrade.sh or vpnupgrade_centos.sh script. Make sure to edit the SWAN_VER variable to the version you want to install, within the script.
How to Uninstall the VPN Server in Linux
To uninstall the VPN installation, do the following.
On RHEL/CentOS
Then open /etc/sysconfig/iptables configuration file and remove the unneeded rules and edit /etc/sysctl.conf and /etc/rc.local file, and remove the lines after the comment # Added by hwdsl2 VPN script, in both files.
On Debian/Ubuntu
Next, edit /etc/iptables.rules configuration file and remove any unneeded rules. Additionally, edit /etc/iptables/rules.v4 if it exists.
Then edit /etc/sysctl.conf and /etc/rc.local files, remove the lines after the comment # Added by hwdsl2 VPN script, in both files. Do not remove exit 0 if it exists.
Optionally, you can remove certain files and directories that were created during the VPN set up.
Generate two ssh keys for git. To set up a site-to-site IPSec-based VPN with Strongswan, check out our guides:
Reference: https://github.com/hwdsl2/setup-ipsec-vpn
Pre Shared Key Authentication
At this point, your own VPN server is up and running. You can share any queries or give us feedback using the comment form below.