Generate 448 Bit Encryption Key
RandomKeygen is a free mobile-friendly tool that offers randomly generated keys and passwords you can use to secure any application, service or device. KEY RandomKeygen - The Secure Password & Keygen Generator. Blowfish is a 16 round feistel chiper that has key lenght from 32 to 448-bit and use large key dependent s boxes. Blowfish is similar to Cast 128 structuraly. In blowfish, every line represents 32 bits. Two subkey arrays are kept the 18 entry P-array and four 256-entry S boxes, which takes 8 bit input while producing 32 bit output. It is free algorithm available to everyone. Blowfish algorithm has gained lots of popularity especially due to its free license. It uses a variable lenght key, from 32 to 448-bit, although most of commercial and non comercial products uses for the strongest 448 bit encryption with blowfish.
-->Creates an encryption key that is used for transparently encrypting a database. For more information about transparent database encryption, see Transparent Data Encryption (TDE).
Syntax
Arguments
WITH ALGORITHM = { AES_128 AES_192 AES_256 TRIPLE_DES_3KEY }
Specifies the encryption algorithm that is used for the encryption key.
Note
Beginning with SQL Server 2016, all algorithms other than AES_128, AES_192, and AES_256 are deprecated.To use older algorithms (not recommended) you must set the database to database compatibility level 120 or lower.
ENCRYPTION BY SERVER CERTIFICATE Encryptor_Name
Specifies the name of the encryptor used to encrypt the database encryption key.
ENCRYPTION BY SERVER ASYMMETRIC KEY Encryptor_Name
Specifies the name of the asymmetric key used to encrypt the database encryption key. In order to encrypt the database encryption key with an asymmetric key, the asymmetric key must reside on an extensible key management provider.
Remarks
A database encryption key is required before a database can be encrypted by using Transparent Database Encryption (TDE). When a database is transparently encrypted, the whole database is encrypted at the file level, without any special code modifications. The certificate or asymmetric key that is used to encrypt the database encryption key must be located in the master system database.
Database encryption statements are allowed only on user databases.
The database encryption key cannot be exported from the database. It is available only to the system, to users who have debugging permissions on the server, and to users who have access to the certificates that encrypt and decrypt the database encryption key.
/acdsee-pro-7-serial-key-generator.html. The database encryption key does not have to be regenerated when a database owner (dbo) is changed.
A database encryption key is automatically created for a SQL Database database. You do not need to create a key using the CREATE DATABASE ENCRYPTION KEY statement.
Permissions
Requires CONTROL permission on the database and VIEW DEFINITION permission on the certificate or asymmetric key that is used to encrypt the database encryption key.
Examples
For additional examples using TDE, see Transparent Data Encryption (TDE), Enable TDE on SQL Server Using EKM, and Extensible Key Management Using Azure Key Vault (SQL Server).
The following example creates a database encryption key by using the AES_256 algorithm, and protects the private key with a certificate named MyServerCert.
See Also
Transparent Data Encryption (TDE)
SQL Server Encryption
SQL Server and Database Encryption Keys (Database Engine)
Encryption Hierarchy
ALTER DATABASE SET Options (Transact-SQL)
ALTER DATABASE ENCRYPTION KEY (Transact-SQL)
DROP DATABASE ENCRYPTION KEY (Transact-SQL)
sys.dm_database_encryption_keys (Transact-SQL)
You will have to generate a private and a public encryption key in order to securely send the order information to FastSpring.
There are two ways on how to generate these keys. The easy way or the long way. The easy way is only possible, if your server is supporting openssl functionalities needed for encryption key generation. These openssl functionalities will be detected by the plugin and so, depending on your server, you will either see the “Generate private and public key” button in the plugin settings page or you wont. If you see the button, then you will be able to use the easy way, if you don’t then please look at the instructions for the long way.
Easy way
- click on the “Generate private and public key” button in the plugins settings
- if the key generation was successful, dismiss the alert message and download the public-key.pem file, by clicking on the “Download private and public key” link
- save the plugin settings
- login to your FastSpring dashboard and navigate to Integrations » Store Builder Library. Upload the public-key.pem file to the Public Certificate option.
That’s it! 🙂
Long way
The private and public keys will have to be generated on your computer, so let’s look at how to generate them.
Generate the private/public keys
The generation of these private/public keys differ, depending on which computer operating system you are using. Please follow the instructions for the OS your computer is using.
macOS and Linux
On macOS and on Linux, you should open the terminal program and execute the commands displayed below:
Create a 2048-bit RSA private key. Don’t share this key with anyone, use it only in the EDD FastSpring plugin settings. This key will be used to encrypt the orders. Use this command to generate the privatekey.pem file which will contain your private key. The file will be created in the position, that the terminal is currently located in (usually your home directory).
openssl genrsa -out privatekey.pem 2048
Create a 2048-bit RSA public key. Only share this key with FastSpring. FastSpring will use your public key PEM file publiccert.pem to decrypt the orders. The file will be created in the position, that the terminal is currently located in (usually your home directory). After you run this command a few short questions will be presented to you, which you can skip, by hitting “enter” key for each of them.
openssl req -new -key privatekey.pem -x509 -days 3650 -out publiccert.pem
Now that you have generated these keys, you have to configure the EDD FastSpring plugin and the FastSpring Dashboard, so look at these instructions in the sections below.
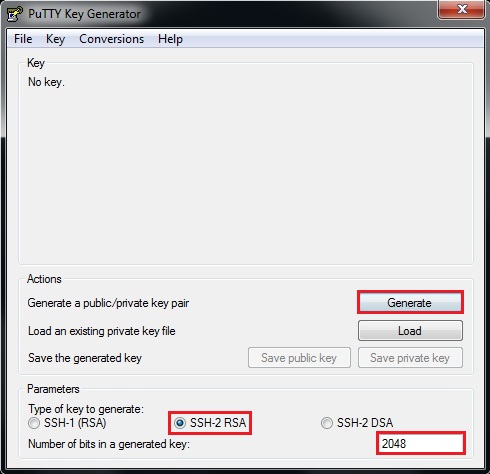
Windows
For generation of these private/public keys your computer needs OpenSSL. Windows does not have that installed by default, so we will have to do that ourselves.
- Go to this website: https://slproweb.com/products/Win32OpenSSL.html
- In the “Download Win32 OpenSSL” section download the latest appropriate “Light” version of the OpenSSL installer. By “appropriate” I mean the version of Windows you are using (32bit or 64bit). I’m using the 64-bit Windows, so at the time of writing this, the latest version to download is “Win64 OpenSSL v1.1.0f Light”.
- Install the downloaded installer file as you would any other windows application (leave the default installation path, because it will be needed later on). In the last step, you can uncheck the donation option and click on “Finish”.
So, the OpenSSL is now installed on your Windows computer and we can generate the private and public keys.
Click on your Windows start button and search for “Command Prompt” (cmd), right click on the “Command Prompt” and choose to “Run as administrator”. Click on “yes”, when the window for the administration conformation pops up.
Copy and paste this command into the cmd and hit enter (this will position the cmd location to your desktop, where we will generate the private/public keys):
cd %userprofile%Desktop
Depending on which version of Windows you have and therefore which version of OpenSSL you installed, you will have to use a specific path to the OpenSSL executable.
By default the paths are:
- If you installed the win32 version, the path will be:
C:OpenSSL-Win32binopenssl.exe - If you installed the win64 version, the path will be:
C:OpenSSL-Win64binopenssl.exe
Generate 448 Bit Encryption Key Download
I’m using the win64 version, so I’ll use that path in the example, if you are using the win32, then just change the “64” in the path to “32”.
Create a 2048-bit RSA private key. Don’t share this key with anyone, use it only in the EDD FastSpring plugin settings. This key will be used to encrypt the orders. Use this command to generate the privatekey.pem file which will contain your private key.
C:OpenSSL-Win64binopenssl.exe genrsa -out privatekey.pem 2048
Create a 2048-bit RSA public key. Only share this key with FastSpring. FastSpring will use your public key PEM file publiccert.pem to decrypt the orders. After you run this command a few short questions will be presented to you, which you can skip, by hitting “enter” key for each of them. Set vendor keys kindle fire 5th generation.
C:OpenSSL-Win64binopenssl.exe req -new -key privatekey.pem -x509 -days 3650 -out publiccert.pem
Now that you have generated these keys, you have to configure the EDD FastSpring plugin and the FastSpring Dashboard, so look at these instructions in the sections below.
EDD FastSpring settings
Open the privatekey.pem file you generated earlier with a text editor (right-click to the file and choose to open with any text editor like Sublime Text or native text editor of your OS). Copy the content of this file.
Go to your WordPress admin dashboard and navigate to the EDD FastSpring plugin settings (Downloads » Settings » Payment Gateways » FastSpring).
Generate 448 Bit Encryption Key Software
Paste the private key content into the Private encryption key setting. Save the settings.
FastSpring dashboard configuration
Login to your FastSpring dashboard and navigate to Integrations » Store Builder Library. Upload the publiccert.pem file to the Public Certificate option.
1024 Bit Encryption
If you have any issues with generating these keys or questions, you can always contact our support and we will help you out 🙂